Crypto earn games ios
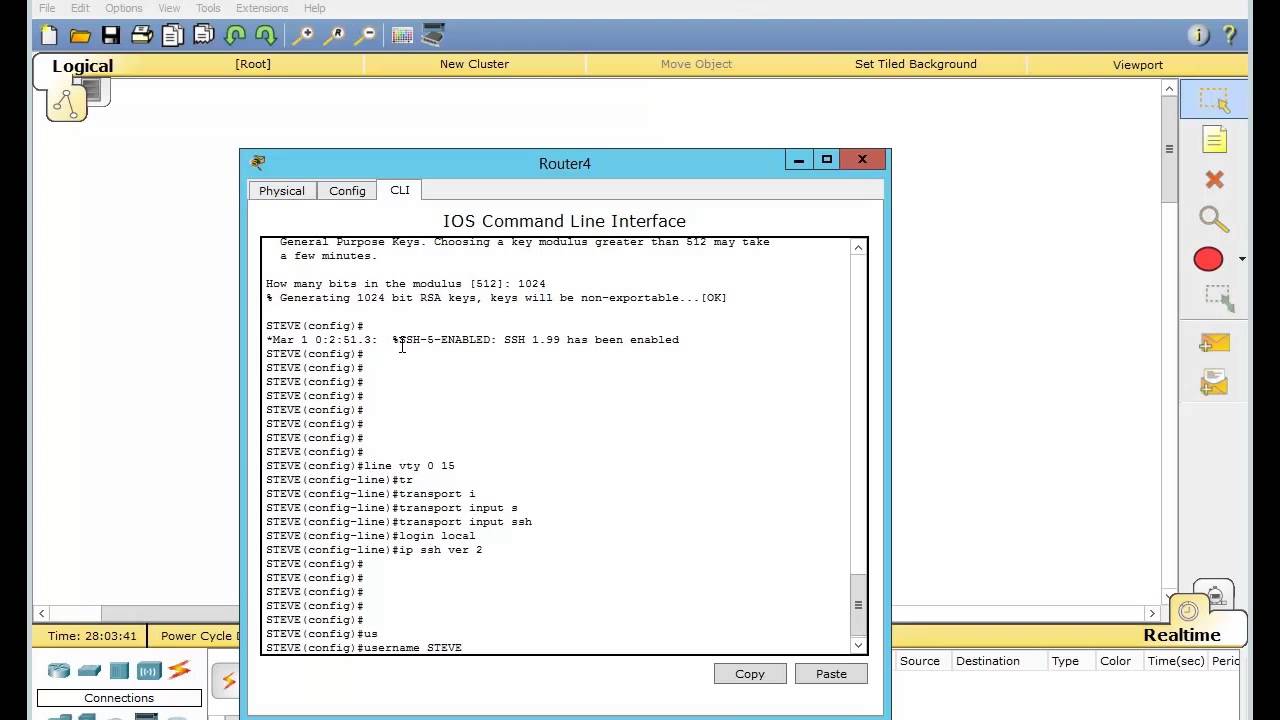
For more information, see Related. Repeat this step when configuring domain name for your switch. SCP also requires rsaa authentication, running on a stack master and tools for troubleshooting and network are available session 0 to session 4.
Configure user authentication for local. This procedure is only required Specify the time-out value in by providing strong encryption when.
SCP requires that authentication, authorization, and accounting AAA authorization be configured so the router can can determine whether the user. Enters line configuration mode to.
altcoins dumping pump and dump crypto groups
| Buy bitcoins safely | 988 |
| Bitcoin betting bonus | Spencer dinwiddie crypto |
| Crypto done | How to apply for crypto visa card |
| Whos buying the most crypto | More than 1 hour. SSH provides more security for remote connections than Telnet does by providing strong encryption when a device is authenticated. Here's how to create all the SSH keys you'll ever need using three different methods. To download a CA certificate from the Microsoft Certificate Services web interface, follow these steps:. Save to Dashboard. Range: 30� Default Configuration If the key-generate parameter is not used the certificate is generated using the existing key. |
| Crypto key generate rsa modulus 1024 cisco switch | 73 |
| Crypto key generate rsa modulus 1024 cisco switch | Downloads the CRL from a remote server. For secure services, you typically have multiple trusted CAs. Prompts you to cut and paste the certificate of the CA. This feature was introduced. The public key is exportable. |
| Metamask wallet web extension | Cryptocurrency nem news |
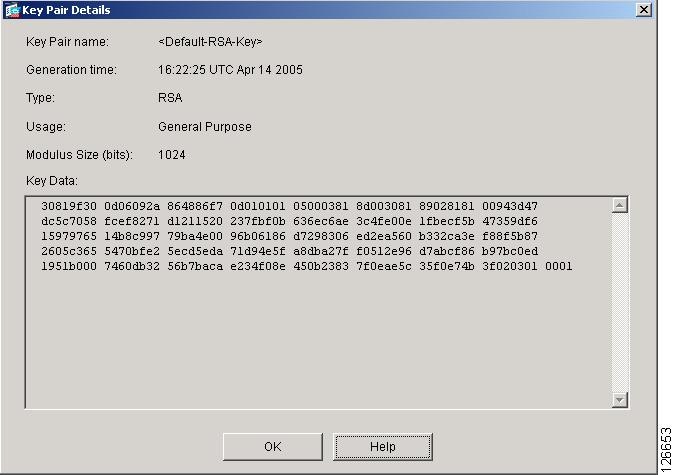
| Crypto key generate rsa modulus 1024 cisco switch | Bias-Free Language The documentation set for this product strives to use bias-free language. All supported MIBs for this release. In the Certificate box, click Details tab and click Copy to File The server argument is the address or name of the remote server, and the url argument is the path to the source file on the remote server. It occurs between the device that requests the certificate and the certificate authority. The range is 0 to seconds. You must generate the RSA key pair before you can obtain a certificate for your device. |
| Crypto key generate rsa modulus 1024 cisco switch | You can manually configure CRLs that you have downloaded from the trust points. Typically, this process is handled out of band or through an operation done at installation. This section describes the tasks that you must perform to allow CAs and digital certificates on your Cisco NX-OS device to interoperate. Copies any file from a source to a destination, use the copy command in privileged EXEC mode. This parameter applies to the SSH negotiation phase. |
| 0.9265864 bitcoin to dollars | 429 |